What is expected from the Audit Trail of a Computerized System
In this article, we analyze what is expected from the audit trail of a computerized system and we show a practical example of how to carry out the audit trail management


Well-managed audit trails are key indicators of good internal business controls. The audit trails have gone from being manual to automated electronic records that make the information history more accurate, easily accessible and usable.
The Audit Trail of a Computerized System is a fundamental tool to have control of the information and to detect and mitigate in time violations of data security, data corruption or the incorrect use of information. And it requires commitment from the top down, from management levels, affected departments and the IT team.
In this article, we will review what the audit trail of a computerized system should include and a proposal for audit trail management for regulated computerized systems.
What is an audit trail
Audit trails are secure electronic records that allow the reconstruction of events related to the creation, modification or deletion of electronic records.
These records provide supporting documentation and history to authenticate operational and security actions or to detect and mitigate deviations. That is, they provide proof of compliance and operational integrity. They are verified in the validation of the computerized system; an audit trail is a tool to maintain the information and the integrity of the system.
What the audit trail of a computerized system should include
Regulation
Both the FDA and the EMA recommend that companies adopt a risk-based approach when determining where to apply (master data management and operations) the audit trail of a computerized system.
According to the recommendations of the EMA, in reference to the audit trail of a computerized system, the regulations of Annex 11 of Eudralex establish that “consideration should be given, based on a risk assessment, to incorporating into the system the creation of a record of all changes and deletions relevant to GMP (a system-generated audit trail)”.
Normative requirements
Requirements of the audit trail of a computerized system:
- In the register of regulated tasks, the person, system or equipment that generates the data must be identified. To make possible the fulfillment of this requirement, the system administrators are requested to correctly codify the users of the system and the process equipment integrated with the system, so that the code can uniquely identify as the user or equipment.
- In the register of regulated tasks, the person or system that carries out the activity generates or modifies data must be identified.
- In the register of regulated tasks, the necessary data and metadata should be recorded.
- Data and metadata associated with the audit trail record: date/time, user, affected entity, new value, old value and reason for the change (for modifications and removals).
- Both original data and the subsequent modifications and the results generated by the system will be available.
Auditory trail system features
Audit trails are mainly used to guarantee the integrity of electronic records. According to the information provided by the regulations and good practice guidelines, the audit trail system must meet the following characteristics:
- Available: audit trails must be maintained in a way that ensures they are always available to regulatory agencies in a format that can be copied and reviewed.
- Automatic: the entries of the audit trail cannot be updated manually by the users. The computer system must capture them automatically when an electronic record is created, modified or deleted.
- Custodial: the audit trail must be kept for as long as it is required that the corresponding electronic record lasts.
- Trackable: each entry must be attributable to the person responsible for direct data entry. Updates made to the data records should not hide the previous values and, when required by regulation, the reason for changing the data should also be recorded.
- Contemporary: Each entry must have a timestamp using a controlled clock system that cannot be changed.
- Secure: the audit trail data should be stored securely and should not be editable by any user.
Management proposal of the audit trail
Next, we show a basic proposal of management of the audit trail (AT) of a regulated computerized system (CS).
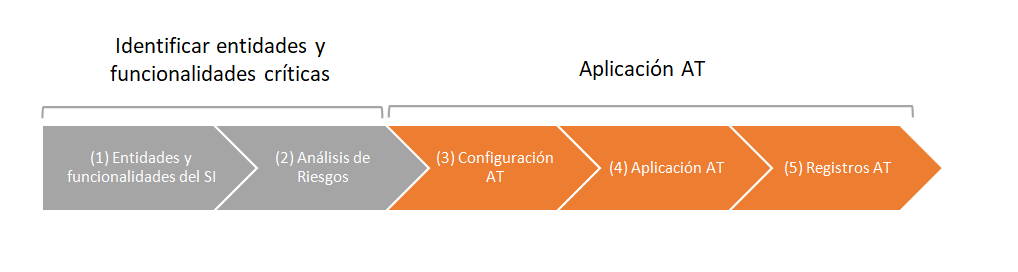
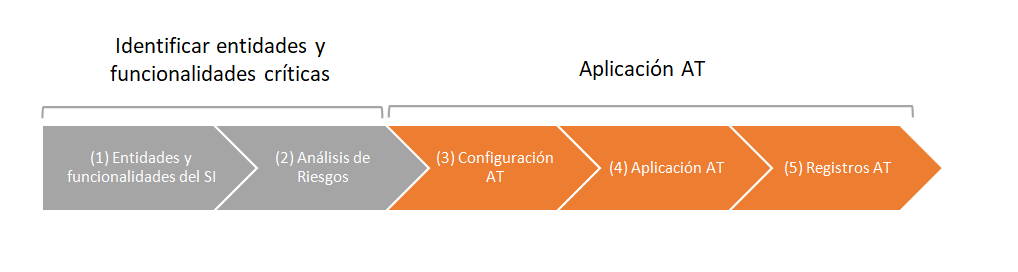
In the first phase, the critical needs and functionalities of the system are identified (master data, processes, users, password and securities, generated, stored and / or processed records).
Audit trail control is not required for the entire application. The risk analysis tool will be used to establish the criticality of master data, processes and securities throughout the validation project.
Entities and processes that are critical must have Audit Trail.
In the second phase, the audit trail system is configured and the registration of events related to the creation, modification or elimination of electronic records is carried out.
Audit trail configuration: the system must have a master data configuration screen with audit trail control. The control can be applied at the general tab level (all fields on the screen will be audited) or by field.
An example can be the configuration of parameters of the article form, suppliers, customers or warehouse types (this data will be decided according to a risk analysis).
The configuration of the audit trail could be the following:
| Family | Type | Field | Description |
| Store | F | – | – |
| Article | C | DESA | Article description |
| Article | C | SECI | Section |
In this example, any changes to the warehouse configuration would be controlled and only the description change in the article´s configuration.
Also, an administration screen will be needed to define the accepted reasons for the change.
Example:
| Code | Description of the reason |
| MANUAL ERROR | Error in the manual error of the data |
| NO CONFORMITY | Change of parameter value due to the study of nonconformity |
| R&D | Change of parameter value due to R&D project |
Application of the audit trail: the system must request the reason for modification or withdrawal. We can associate previously parameterized reasons (so that when the cause is added a drop-down list is shown) and a free description of the reason in order to specify each case.
Records of the audit trail: the system must record the registration, modification or removal of the parameters considered critical for the computerized process.
In this case, you must register:
- Date and time.
- The user who performs the registration, modification or cancellation action.
- The entity in which the changes are made.
- Affected field of the entity. A record will be made per modified field.
- Type of action performed: registration, cancellation or modification.
- Old value and new value.
- The reason why the change has been made. Drop-down list.
- Free text to describe the reason (optional).
Example of an audit trail of a computerized system:
| Date and time | User | Entity | Field | Action | Old value | New value | Reason | Motive description |
| 30/01/2019
13:02:01 |
mgarrote | Article | Description | Modification | Description | Description 2 | NORM | Product registration |
| 30/01/2019
13:22:01 |
mgarrote | Article | Code (ID of the entity) | Deletion | 1 | NA | NORM | Obslete product |
| 30/01/2019
13:33:01 |
mgarrote | Article | Code (ID of the entity) | Creation | NA | 2 | NA | NA |
| 30/01/2019
13:33:01 |
mgarrote | Article | [Field]… | Creation | Value | 2 | NA | NA |
If you need help to configure and implement audit trails in your organization, in Oqotech we have more than 10 years of experience helping companies in regulated sectors to computerize their process, ensure the integrity of their data and validate their computerized systems.
Contact our team of expert consultants.








